Endpoint Detection & Response (EDR)
Experience an elevated level of EDR with our cutting-edge solution. Our comprehensive platform offers unparalleled prevention, advanced threat-hunting, and efficient remediation capabilities. Empower yourself to swiftly and seamlessly counter even the most sophisticated malware attacks.
Elevate Your Company’s Endpoint Detection & Response Stance with Heimdal
Heimdal Endpoint Detection and Response is a powerful security tool that actively monitors, analyzes, and responds to threats in real-time. With advanced detection algorithms and proactive incident response capabilities, it provides robust protection for your enterprise endpoints, ensuring timely threat mitigation and minimizing potential damage.
A Holistic Security
Model
Experience a layered and integrated approach that combines the strengths of all its components, leveraging intelligence across modules to fortify your entire ecosystem. With one unified model, you can effectively hunt, prevent, detect, and respond to threats.
Complete Endpoint
Visibility
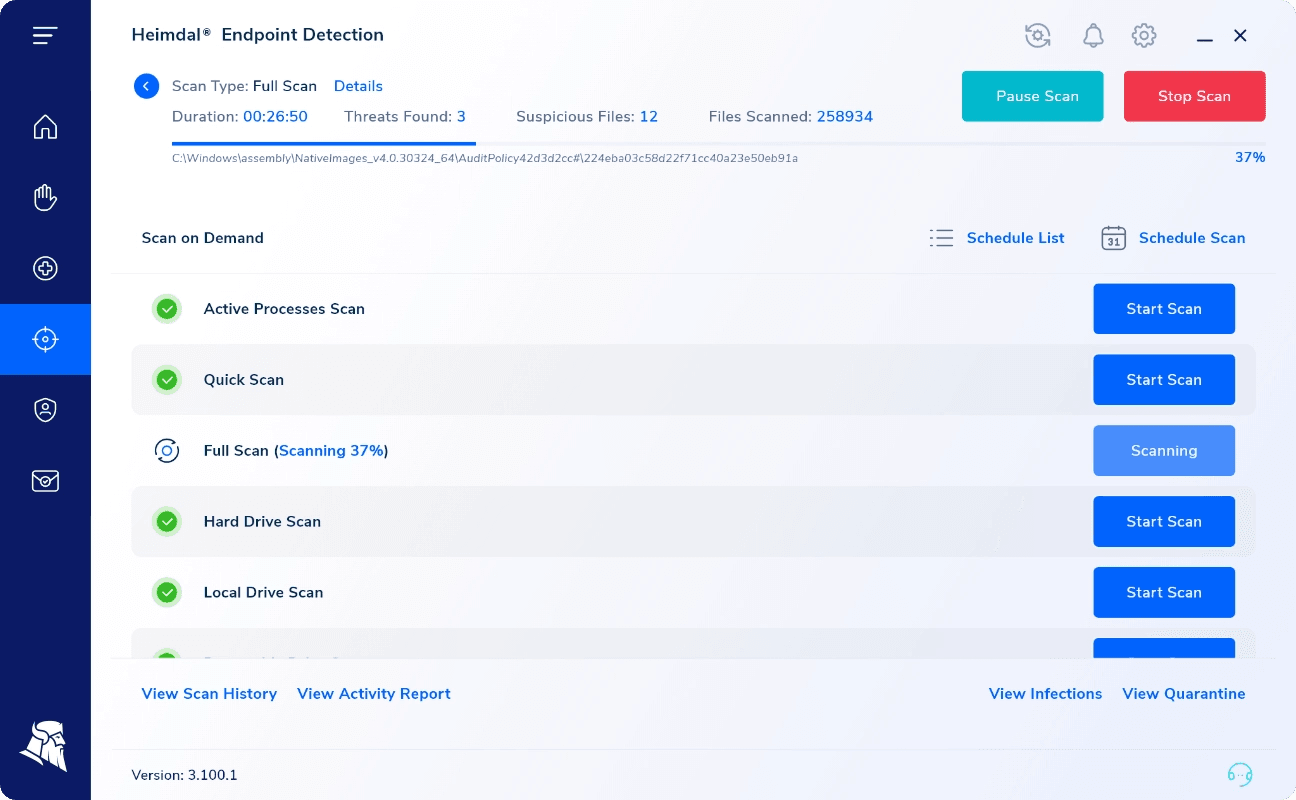
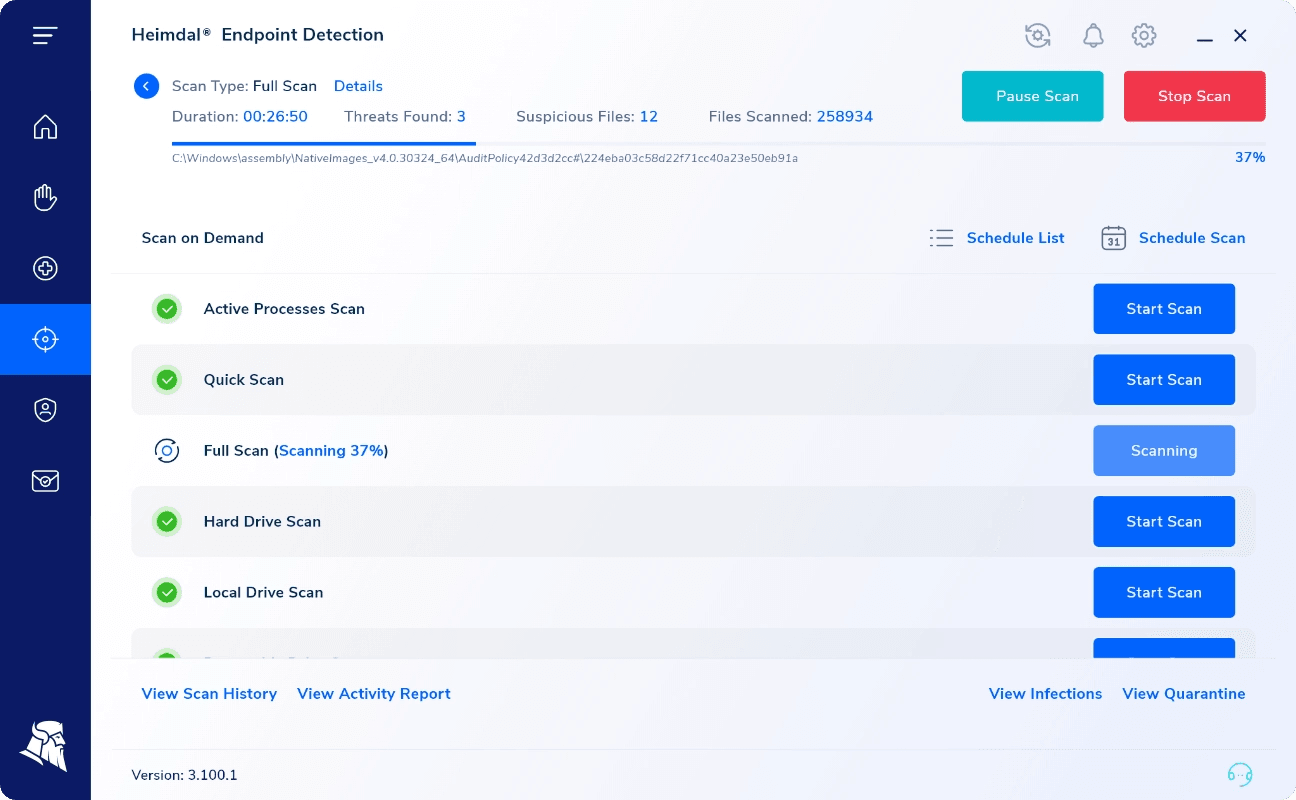
Unlike traditional cybersecurity measures, a unified EDR approach provides unparalleled endpoint visibility, allowing for rapid response in the face of threats. Experience the exceptional capabilities of our suite with proactive prevention, advanced threat hunting, and efficient remediation.
Increased
Productivity
Discover and neutralize all exploits without the need for separate threat-hunting solutions or manual analysis. Seal vulnerabilities and safeguard your digital landscape with unparalleled efficiency – powered by groundbreaking technology that ensures uninterrupted prevention.
Enhance Your Endpoint Security Through
an Integrated Approach
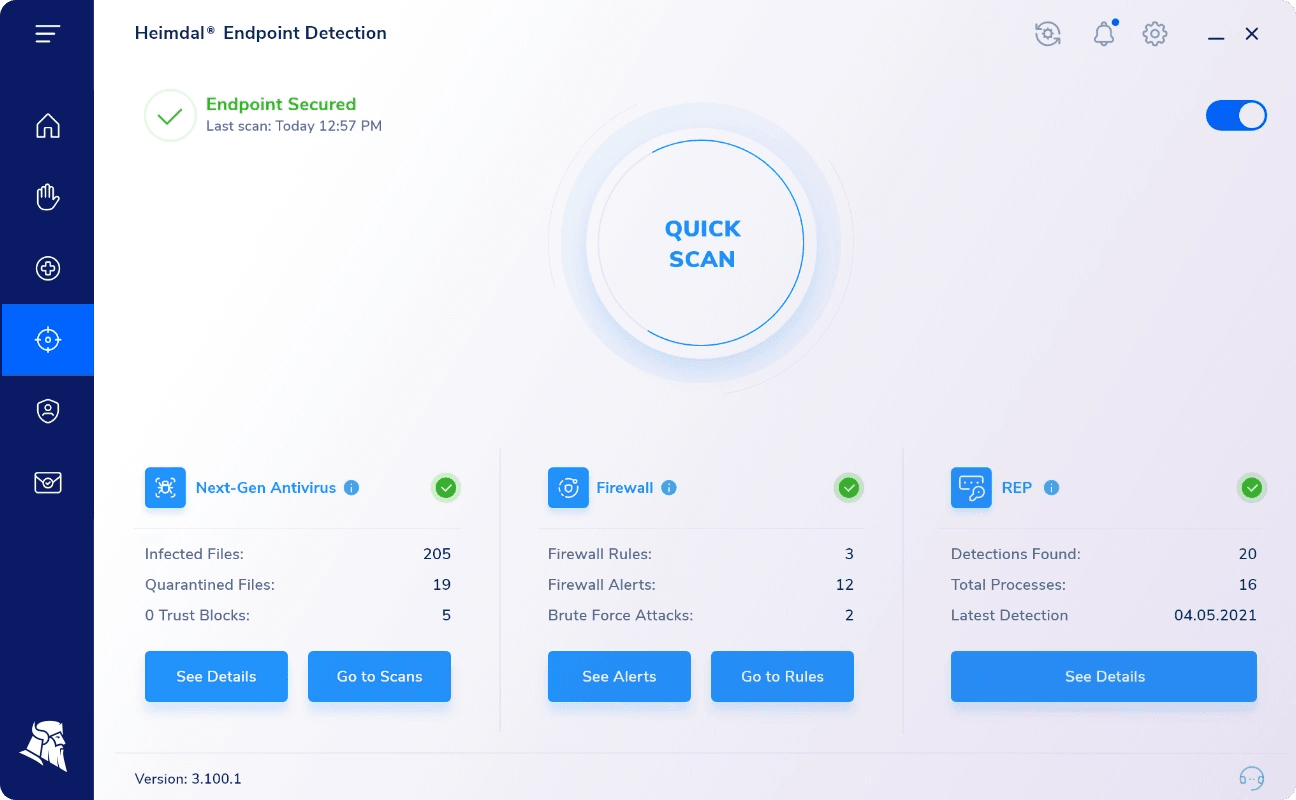
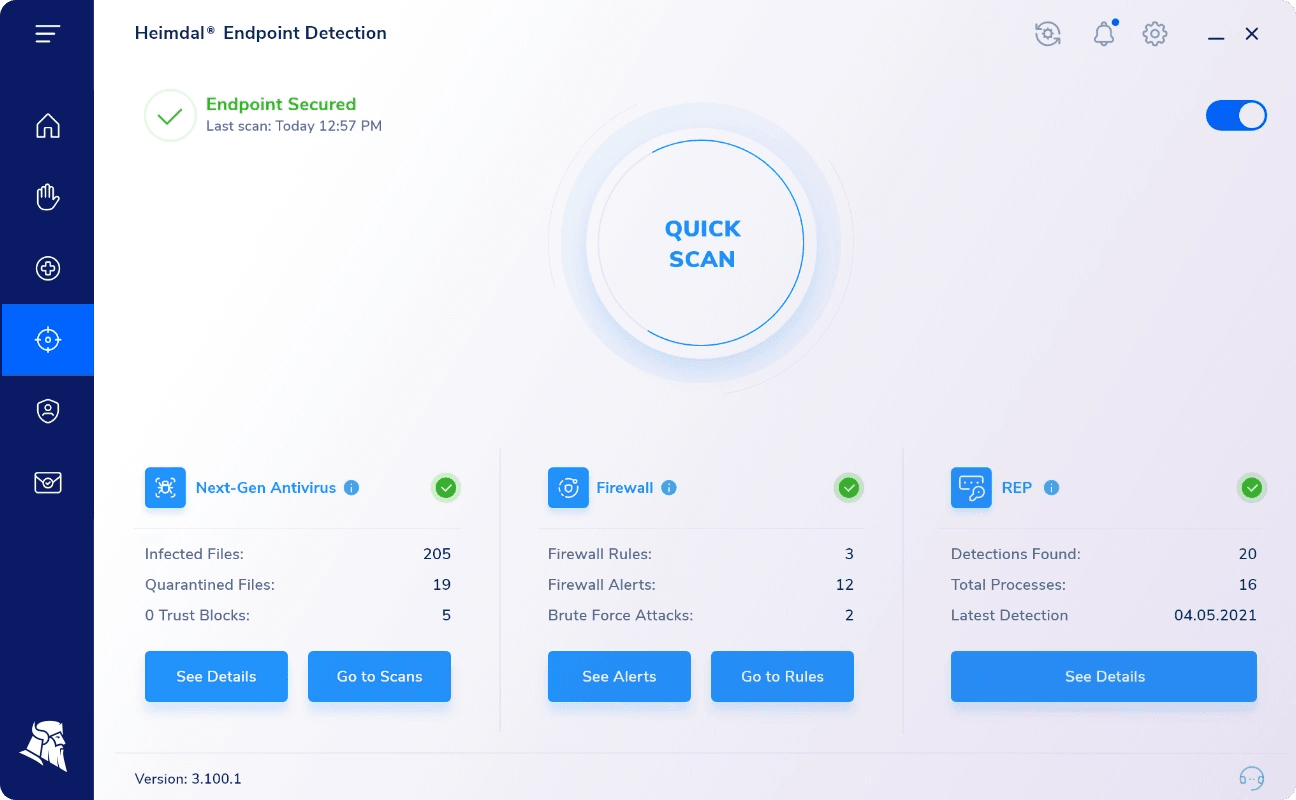
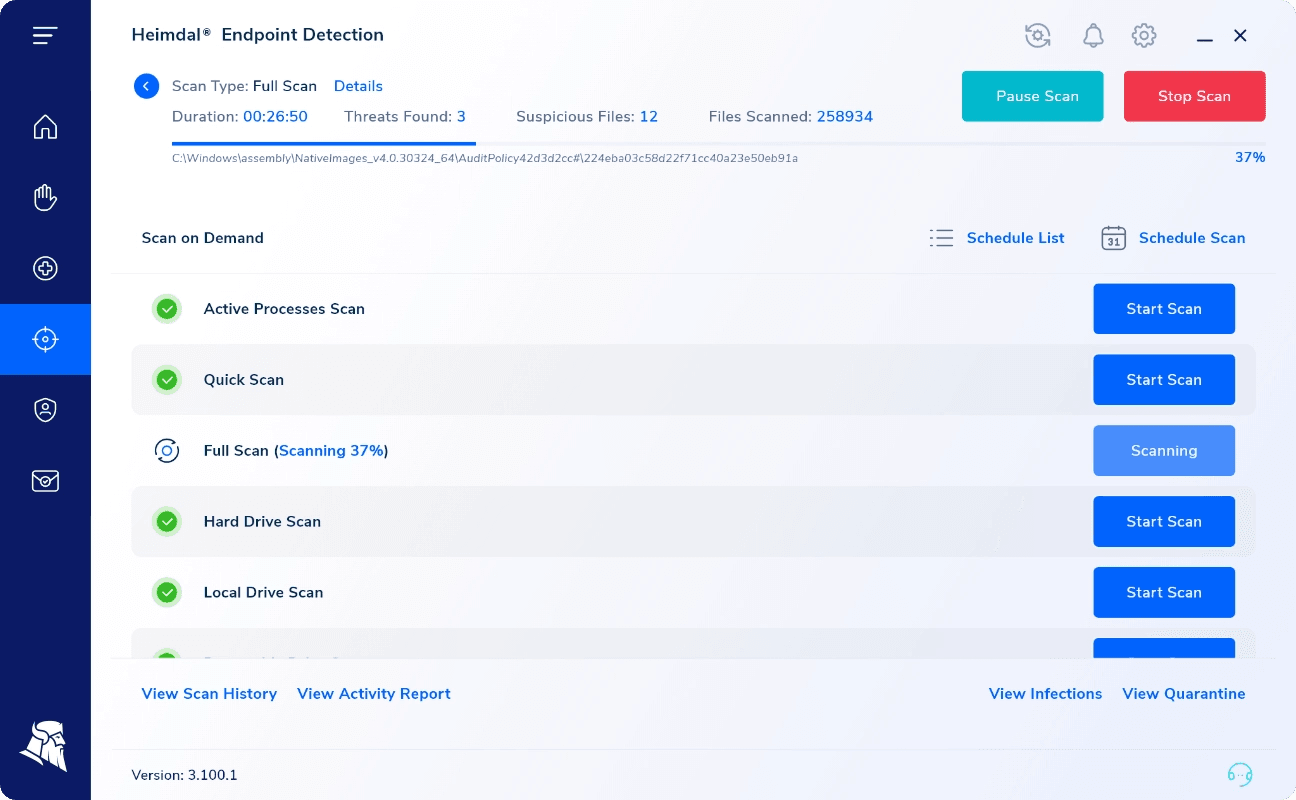
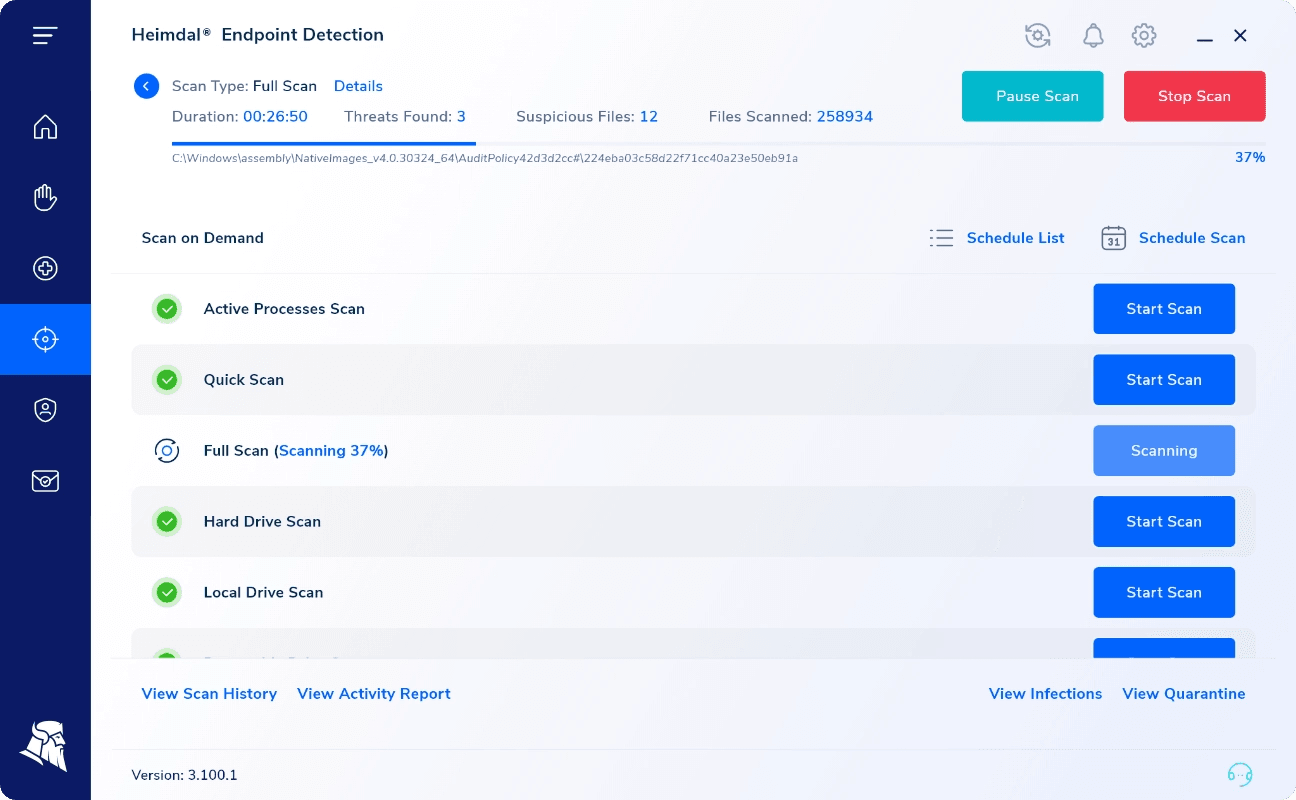
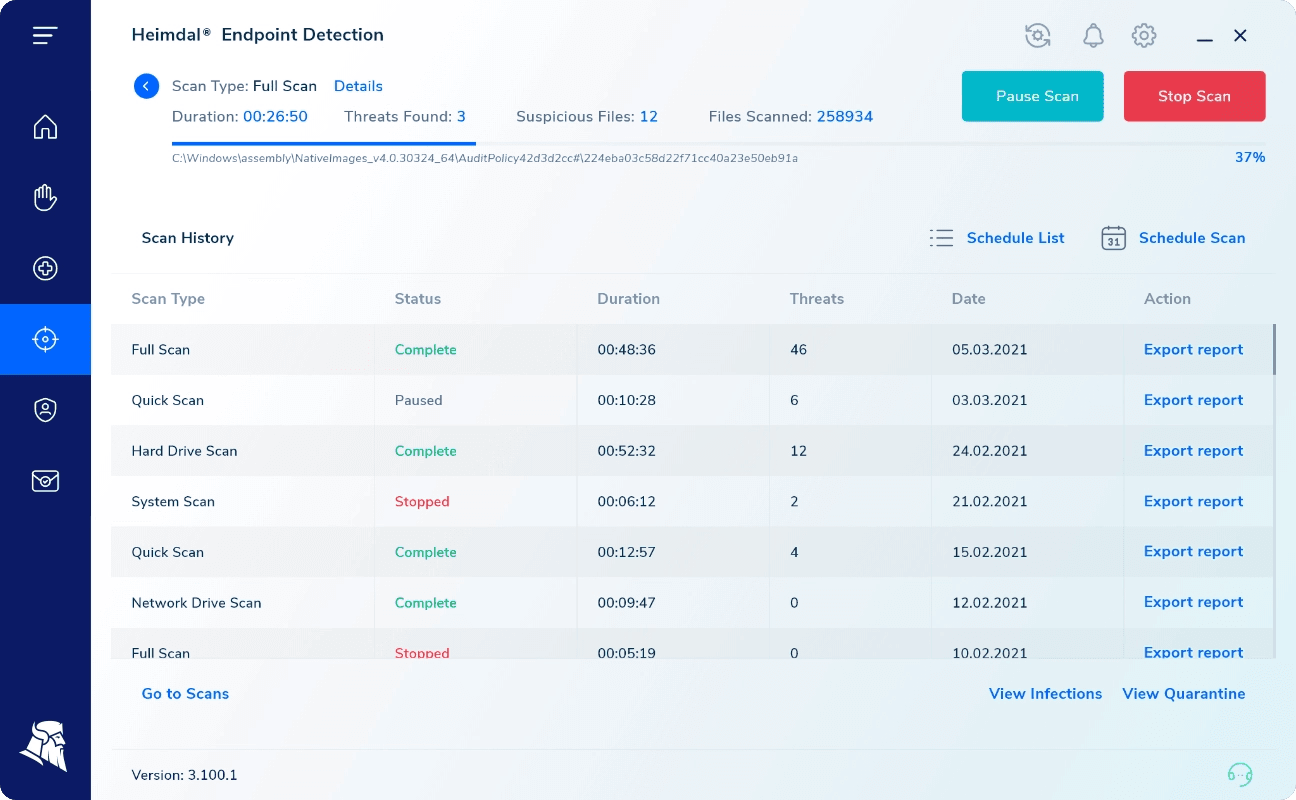
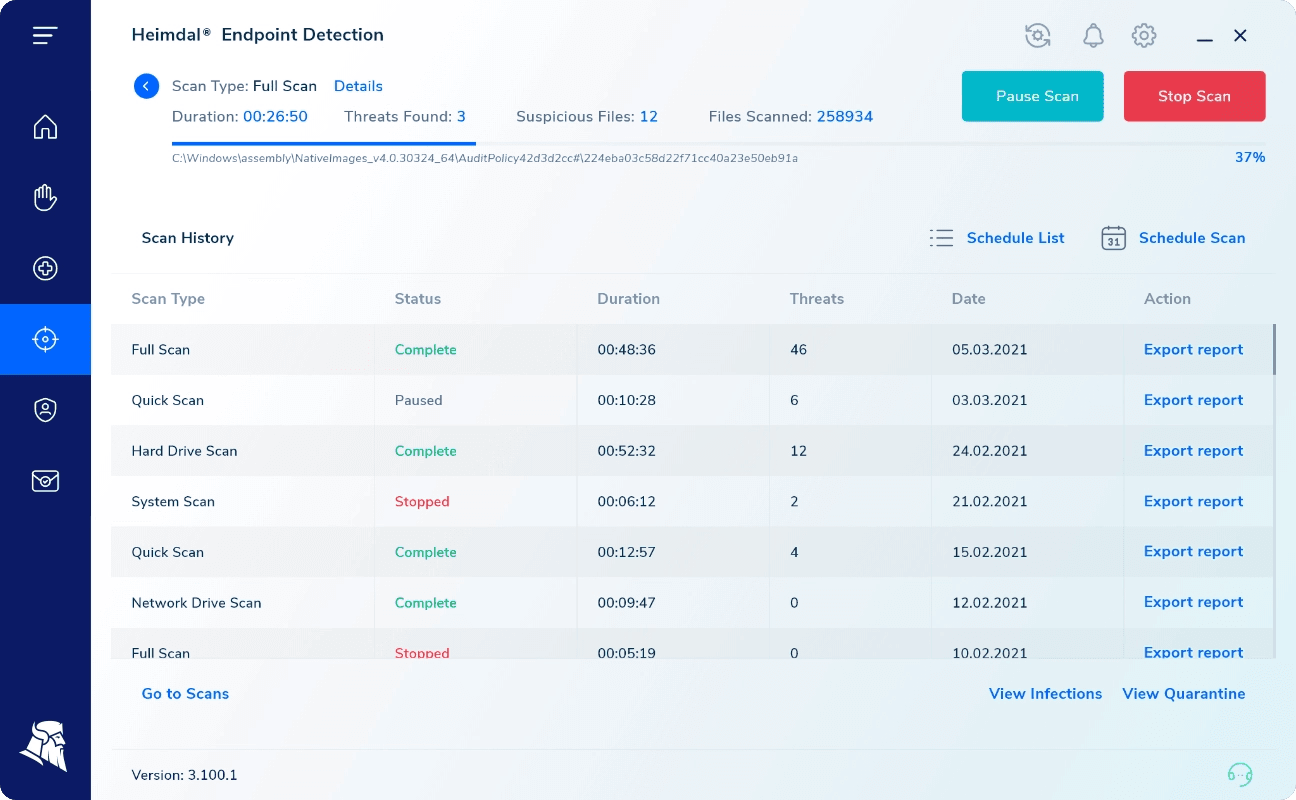
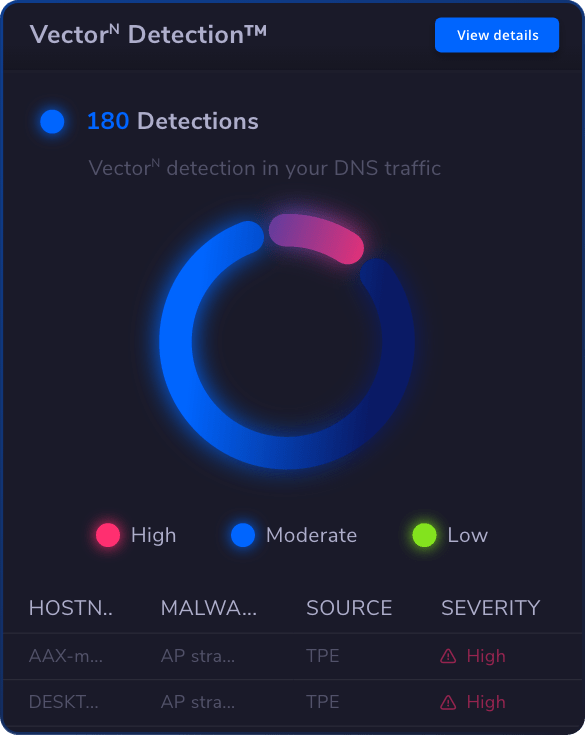
Efficient Threat Tracking & Analysis
Gain comprehensive visibility into endpoint activity through sophisticated data analytics. Swiftly respond to incidents by correlating your data with actionable Threat Intelligence.
Benefit from proactive Indicators of Compromise (IOCs) and improved Indicators of Attack (IOAs), empowering you with a unique EDR capability to mitigate even concealed or unknown malware. Strengthen your defenses and stay ahead of evolving threats.
Advanced Attack Prevention
Our cutting-edge EDR software goes above and beyond traditional security solutions, ensuring robust protection against complex cyber threats. Experience the power of machine learning and AI-driven intelligence, delivering unmatched proactive protection for your endpoints.
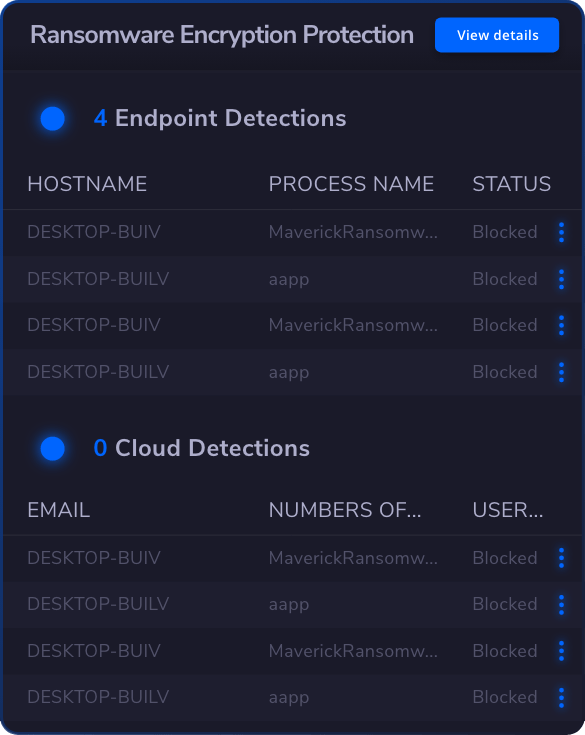
Our EDR software safeguards your network against an array of threats, including advanced ransomware, insider threats, admin rights abuse, APTs, software exploits, brute force attacks, DNS and DoH vulnerabilities, phishing and social engineering, and any other known or unknown threats.
One Agent, Six Solutions
Streamline your security operations with our EDR system, encompassing a comprehensive suite of technologies in a single, lightweight agent. Experience hassle-free deployment that won’t impact system performance, saving you valuable time.
Enjoy the benefits of fully integrated endpoint protection, incorporating a range of next-gen security solutions, all within a fully unified solution that safeguards against all attack vectors.
Secure your enterprise endpoints on all fronts with Heimdal EDR.
Heimdal Endpoint Detection and Response grants you access to all the essential cybersecurity layers your business needs to protect itself against both known and unknown online and insider threats.
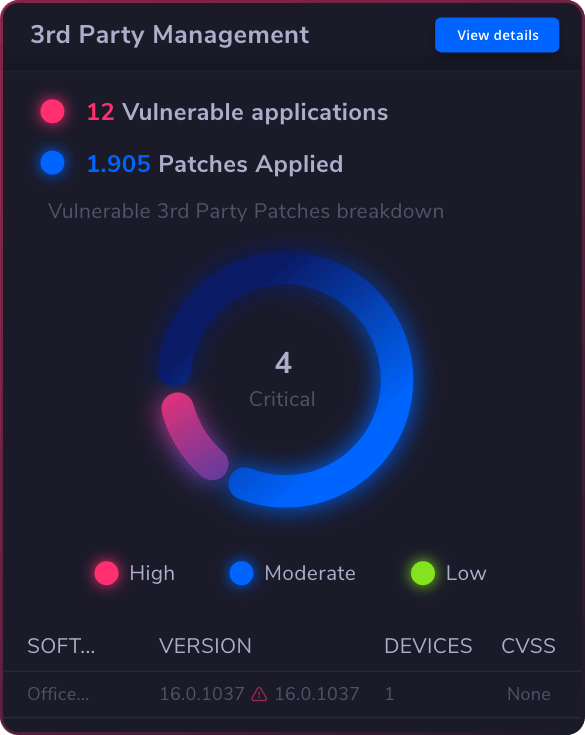
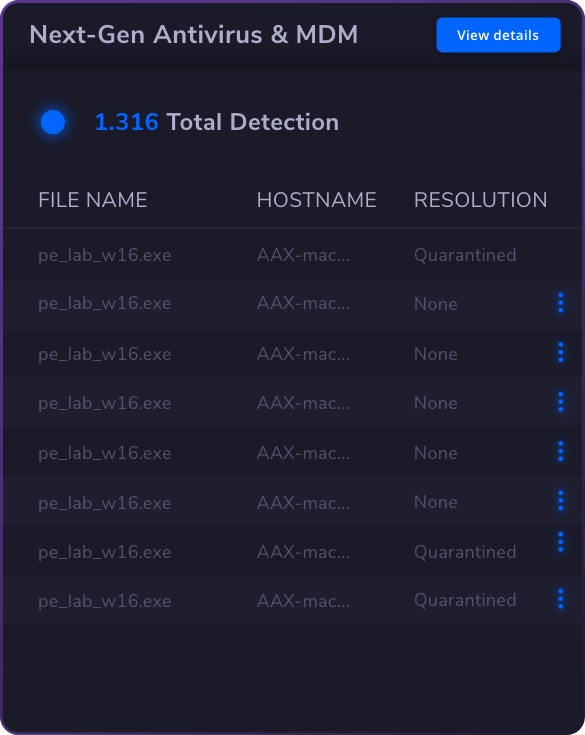
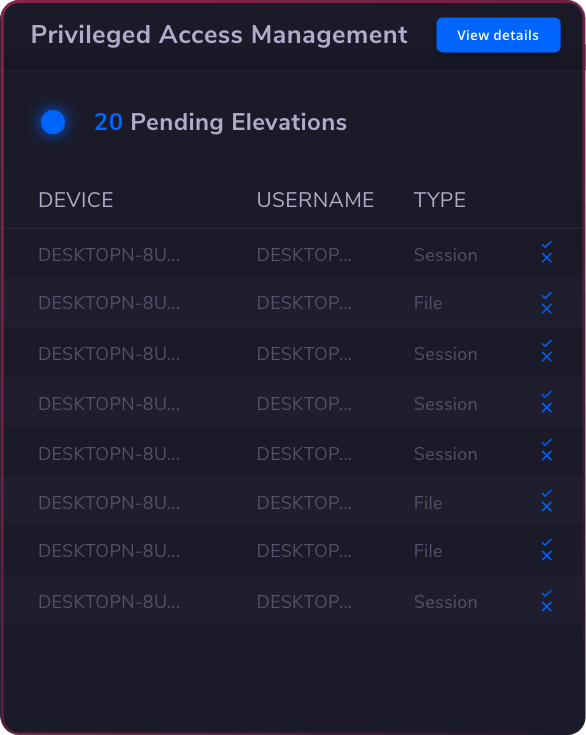
The package combines the most advanced threat-hunting technologies in existence: Next-Gen Antivirus, Privileged Access Management, Application Control, Ransomware Encryption Protection, Patch & Asset Management, and DNS Security.
All working together seamlessly from one agent and one unified platform.

Network
Security

Endpoint
Security

Vulnerability
Management

Privileged
Access
Management
Privileged Access Management
Privilege Elevation & Delegation Management Privileged Account & Session Management Application Control
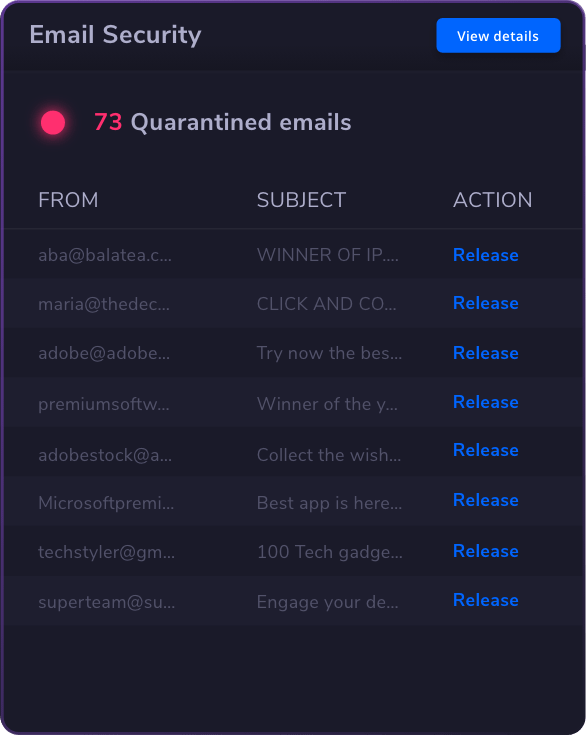
Email &
Collaboration
Security

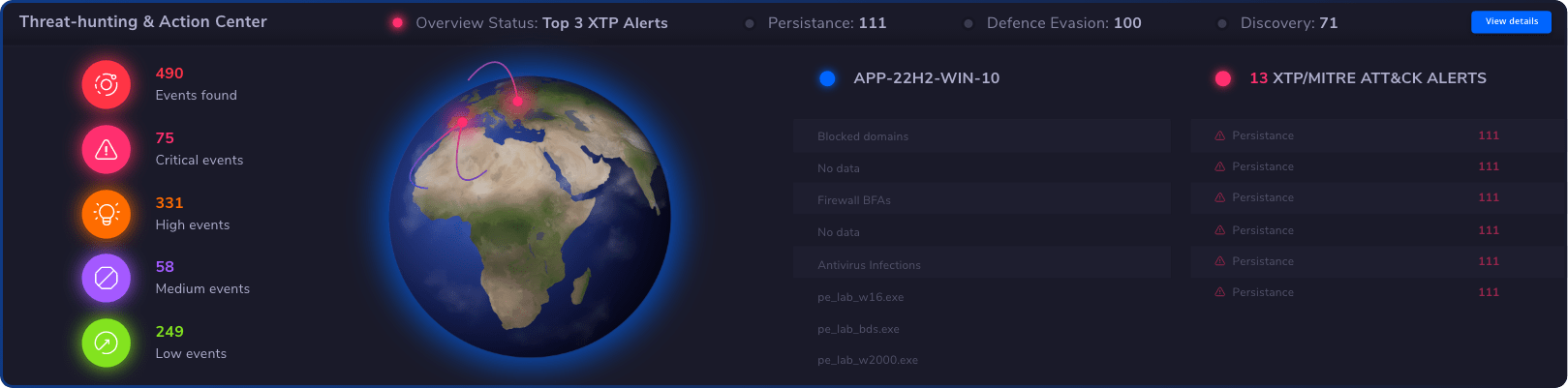
Threat
Hunting
Threat Hunting
Threat-hunting & Action Center
Unified
Endpoint
Management
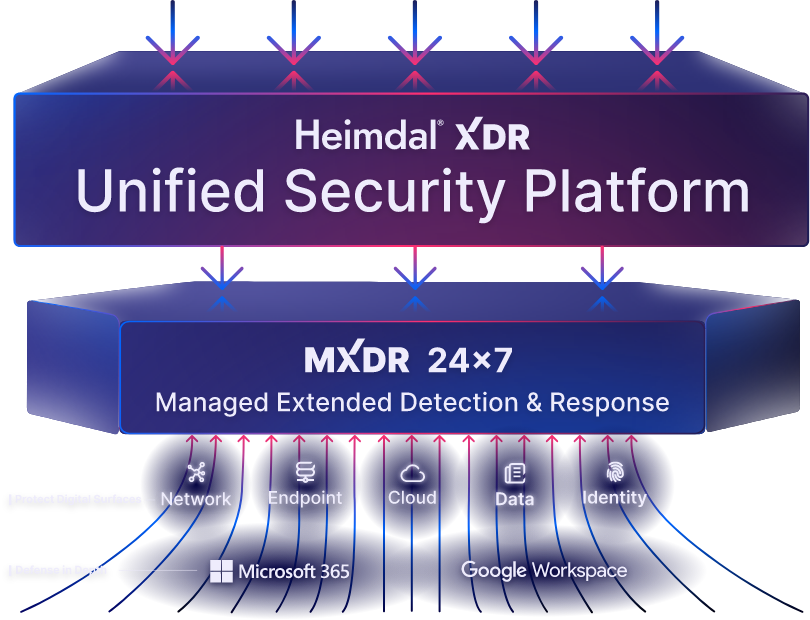
Heimdal XDR
One Platform. Total Security.
One Platform,
Total Security.
Experience the Power of Heimdal XDR the Unified Security Platform that Delivers Comprehensive Protection against Next-gen Threats
See Heimdal XDR in Action:
Schedule a Live Demo Now!



 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management
 Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security










 4.8/5
4.8/5

